Federal Informant James McGibney
Looks like federal informant James "Pissboy" McGibney is back at it again.
Longtime readers will be aware that there is a precedent setting 1st Amendment case with my name on it - Rauhauser v. McGibney. This case, now in its 122nd month, is a torturous read, but the summary is easy. “You may not file a frivolous case in Texas, and then flee to avoid consequences of the Texas Citizens Participation Act when the other party turns up with the best 1st Amendment guy in the state.”
McGibney earned the nickname Pissboy thanks to this 2014 article in Al Jazeera, which he’s tried desperately to suppress. Luckily the Wayback Machine is on duty.
Vigilanteville: James McGibney and his online army.
This case is now headed for its third trip through appellate court in Texas and there has been an irregular sprinkling of signs that he is again active. I don’t mind if he’s getting snitch money framing Kiwi Farms twerps, but I am not going to serve as a stalking horse for him, so this post will serve as a reference for the hapless farm animals he’s trying to victimize.
Attention Conservation Notice:
Contains a grown ass man with an AARP card acting like a juvenile delinquent. Reading this WILL make you dumber.
Federal Informant James McGibney:
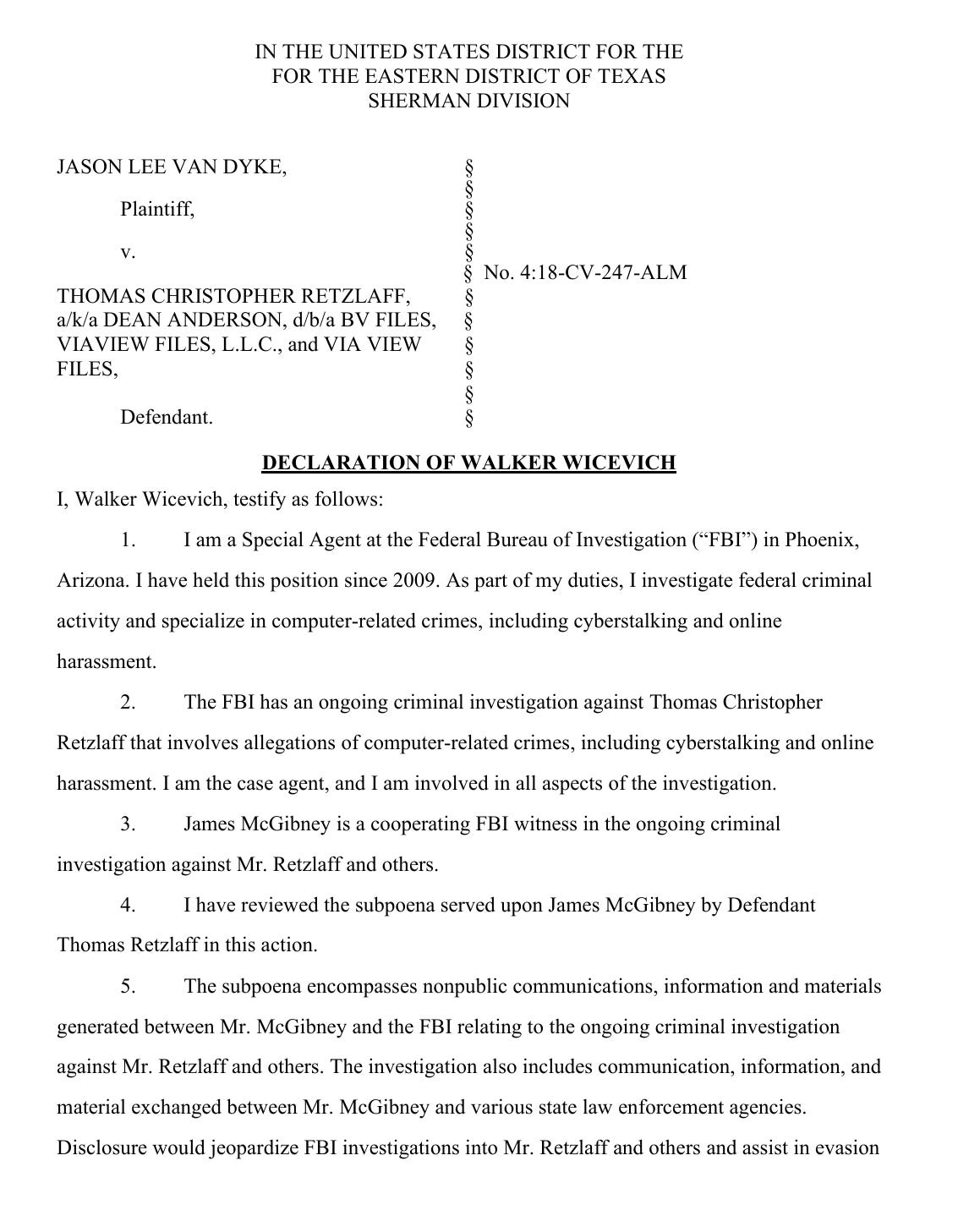
This is a sworn affidavit from FBI special agent Walker Wicevich regarding James McGibney’s true nature.
If you Google a bit you’ll find that Jason Lee Van Dyke was engaged in an assassination plot against my attorney, Jeff Dorrell, and this Tom Retzlaff character, which the FBI broke up. It all settled down when Retzlaff was murdered a year later, and Pissboy dragged our case out another year from that via a court filing indicating he couldn’t testify due to the 5th Amendment concerns, since he was a suspect in Retzlaff’s murder.
I’ve started a public Rauhauser v. McGibney NO. 02-14-00215-CV project on the Neal Rauhauser Document Cloud. Forewarned is forearmed - Document Cloud has been acting like three Porgs in a trench coat for the last week or so. Just be persistent.
Josh Moon’s Digital Cesspool:
Here are some things I have written about Kiwi Farms and its owner, Josh Moon.
Crack Babies Of Kiwi Farms - noticed some dipshits creeping up on me back in April.
Kiwi Farms Crack Baby Butthurt - making fun of dipshits without name checking them, but I’m fairly sure I know who one of them is, and the other is a familiar, albeit moronic persona.
Stochastic Terrorism As A Service - the June 27th, 2021 murder of Near aka David Kirk Ginder was the final straw. I dug until I found signs that Chinese intel might be involved in supporting Kiwi Farms, then sent that off to the Australian Federal Police and the FBI.
Expanding on what I said above, I think it’s excellent news if the FBI has some informants up in the middle of Kiwi Farms and the investigating (read: framing) the CHUDs that inhabit those sites. I’m even cool with James “Pissboy” McGibney getting paid to frame them, like he did with at least two other people.
Roy Arcadio Jimenez aka 5hm00p
But I have zero interest in serving as bait, so I’ve taken some steps like this to ensure that if Pissboy points his tiny tool at me he’ll end up soaking his own leg instead.
Conclusion:
My original lawyer, Jeff Dorrell, died after a long illness on August 23rd, 2021. Tom Retzlaff was murdered September 1st of 2021. The lawyer Pissboy was using in California, Jay Leiderman, died of a heart attack *cough* overdose *cough* on September 7th of 2021.
Earlier today I got the copy of the appellate brief on the case. At the same time a little bird whispered to me that McGibney was trying to whip up an online mob against Lane Haygood, the attorney that took over my case when Jeff Dorrell died.
Given that there’s never NOT been a time when James McGibney was working as an informant, I imagine he’s back at it. Given that I’ve done something that attracts the attention of folks in Tehran, which you can read about in Sounds Of Silence, I’ve accomplished something similar with a right wingers/Russians problem, as seen in MIOS: Russpublicans, and I admitted knowing a bit about SoCal Armenian Extremists Attack UCLA Protesters … well … ya think there might be some feds in that mix?
This is going to be much funnier for me than it will be for anyone dumb enough to get sucked into Pissboy’s framing shop. I’ll leave you with a funny stock photo I found …